Hello everyone, we are all aware about Linux systems, its .bash_history and how it provides information about file locations, passwords passed in command arguments, a variety of scripts and so on.
But did you know, something similar to it now also exists in PowerShell? That’s precisely what I will be sharing about in today’s blog post, everything to know about PowerShell’s history file.
About PSReadLine
The PSReadLine module became the default command line experience for PowerShell v3 and above. It provides a bunch of features, you can read more about module here.
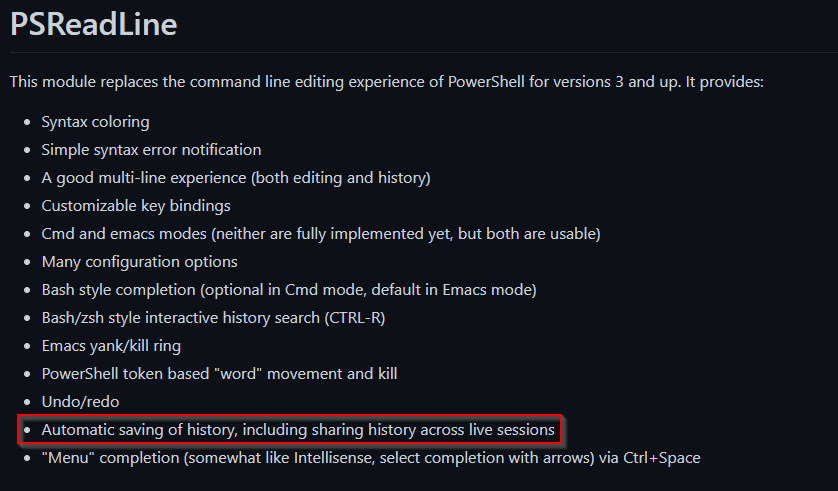
See the red box in the above image, that’s what we’re looking for! PowerShell v3 and over now included a history file which saves all executed commands.
For PowerShell v5 on Windows 10, the default option saves history to a file.
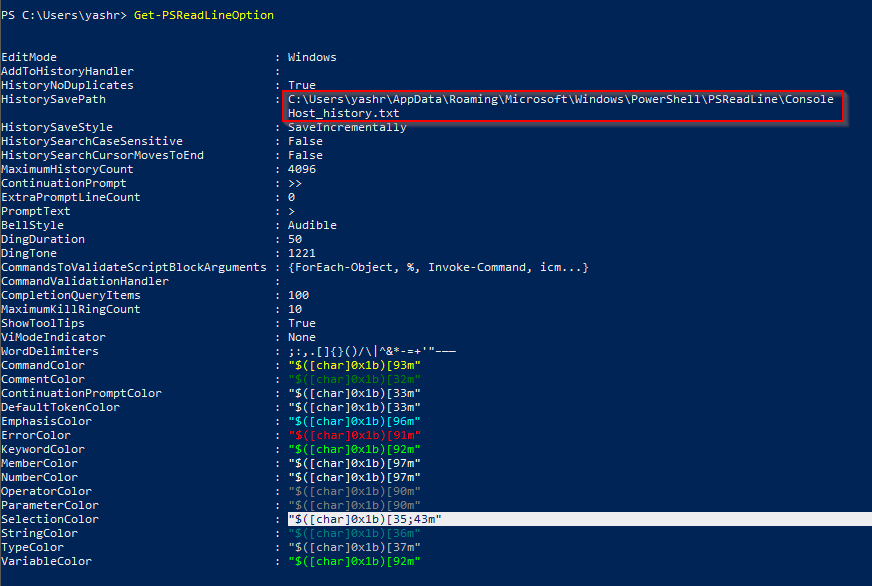
Get-PSReadLineOption
First things first, the name of the file is ConsoleHost_history.txt and the default location is at:
$env:APPDATA\Microsoft\Windows\PowerShell\PSReadLine\
$env:APPDATA can also be written as C:\Users\username\AppData\Roaming if your environment variables don’t work (sometimes the case in reverse shells).
Moving onto some other interesting properties of PSReadLine, we can read all the propterties using the Get-PSReadLinOption
- HistorySavePath – Shows you the file location
- HistorySaveStyle – The way your history file is saved, there are three options:
- SaveIncrementally – Appends the file after each command
- SaveAtExit – Saves all the commands executed in a session upon exit
- SaveNothing – Disables the history file.
- MaximumHistoryCount – The maximum number of entries that will be held in the file (default: 4096)
You can also modify these settings and everything else using the Set-PSReadLineOption cmdlet.
A Sample Output of the Get-PSReadLineOption Command:
Logging Capabilities
Everything I type into a PowerShell terminal gets logged in the history file:

However, anything executed using a “Terminal-less” PowerShell session won’t get logged into the file. A terminal-less PowerShell session would be created in case of remote code executions where a attacker may move from cmd.exe to powershell.exe.
Things you could find
From a Red Teamer’s perspective. things similar to what you would find in a Linux .bash_history
- Executed Commands
- Files being interacted with.
- Passwords (maybe)
- Variables defined while running multi-line code blocks and/or scripts.
That’s all for this post.
Thanks for Reading!
Leave a comment